Playbook: Block Indicators
Description
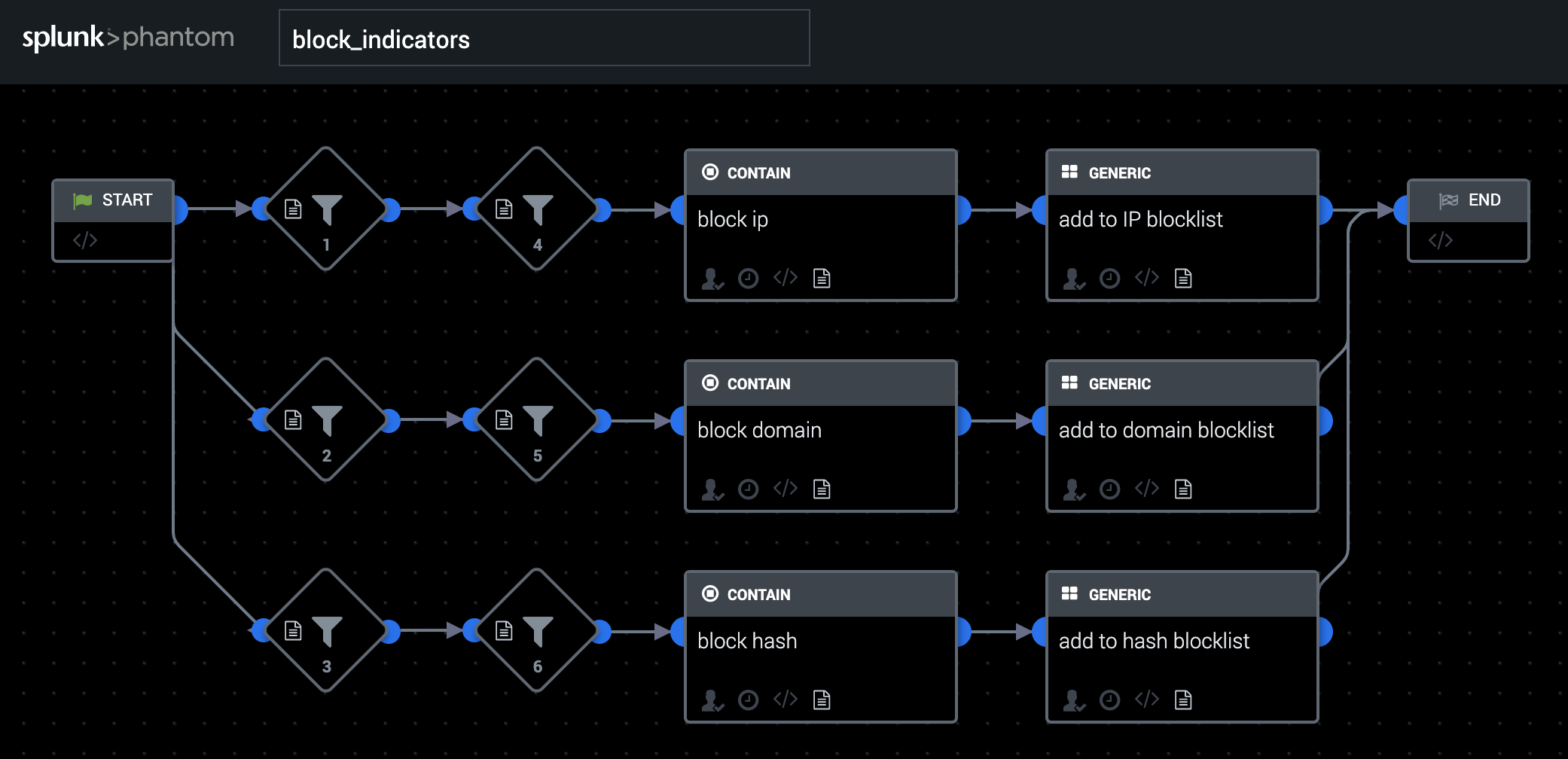
This playbook retrieves IP addresses, domains, and file hashes, blocks them on various services, and adds them to specific blocklists as custom lists.
Apps
Palo Alto Networks Firewall, Carbon Black Response, Cisco Umbrella
How To Implement
This playbook uses the following custom lists: ip_address_blocklist, domain_blocklist, filehash_blocklist. This playbook provides an easy, automated, and straightforward solution to maintaining up-to-date IP address, file, and domain blocklists. The playbook looks for any of the required CEF fields within the container. The CEF value is then cross-referenced with their respective Custom Lists. IP addresses are blocked on a Firewall, while domains are blocked using a blocklist service. The blocking of these two will prevent access to the IOCs. Finally, file hashes are blocked using an endpoint protection service, which will prevent the process from running on affected endpoints within a network. After the IOCs are blocked using various apps, they are added to their respective custom lists as to maintain a running blocklist record.
Explore Playbook
Required fields
-
destinationDnsDomain
-
destinationAddress
-
fileHash
Reference
source | version: 1
