Playbook: CrowdStrike OAuth API Identifier Activity Analysis
Description
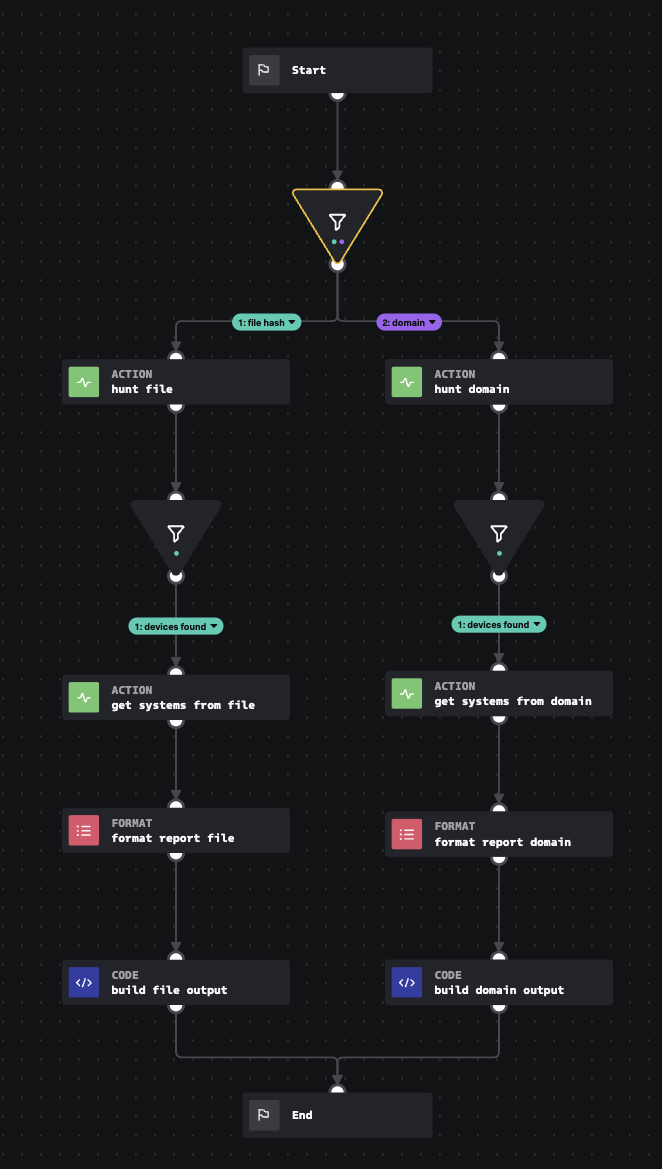
Accepts a file hash or domain name, and asks CrowdStrike for a list of device IDs that have interacted with each. The list of IDs is then sent back to Crowdstrike to get more information, and then produces a normalized output and summary table.
Apps
How To Implement
This input playbook requires the Crowdstrike OAuth API connector to be configured. It is designed to work in conjunction with the Dynamic Identifier Activity Analysis playbook or other playbooks in the same style.
Explore Playbook
Click the playbook screenshot to explore in more detail!
Reference
source | version: 2