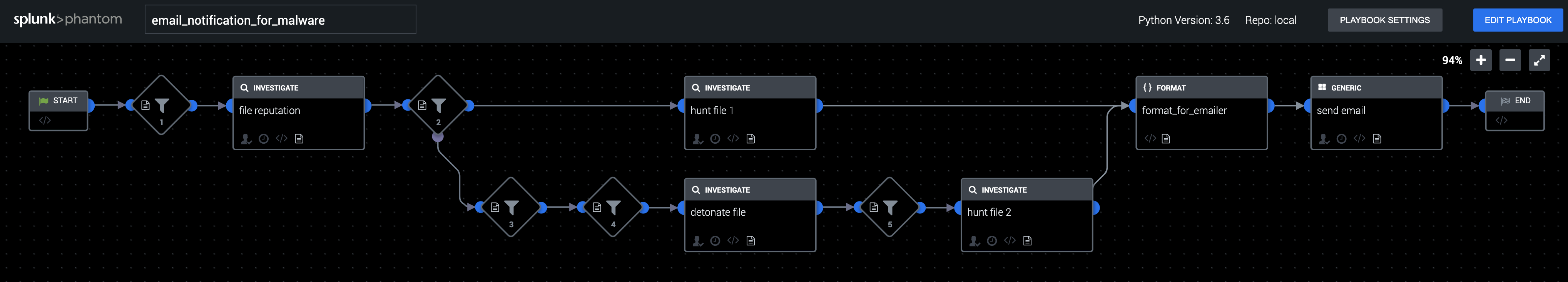
Playbook: Email Notification for Malware
Description
This playbook tries to determine if a file is malware and whether or not the file is present on any managed machines. VirusTotal "file reputation" and PAN WildFire "detonate file" are used to determine if a file is malware, and CarbonBlack Response "hunt file" is used to search managed machines for the file. The results of these investigations are summarized in an email to the incident response team.
Apps
VirusTotal, WildFire, Carbon Black Response, SMTP
How To Implement
Be sure to update asset naming to reflect the asset names configured in your environment.
Explore Playbook
Required fields
-
fileHash
-
vaultId
Reference
source | version: 1
