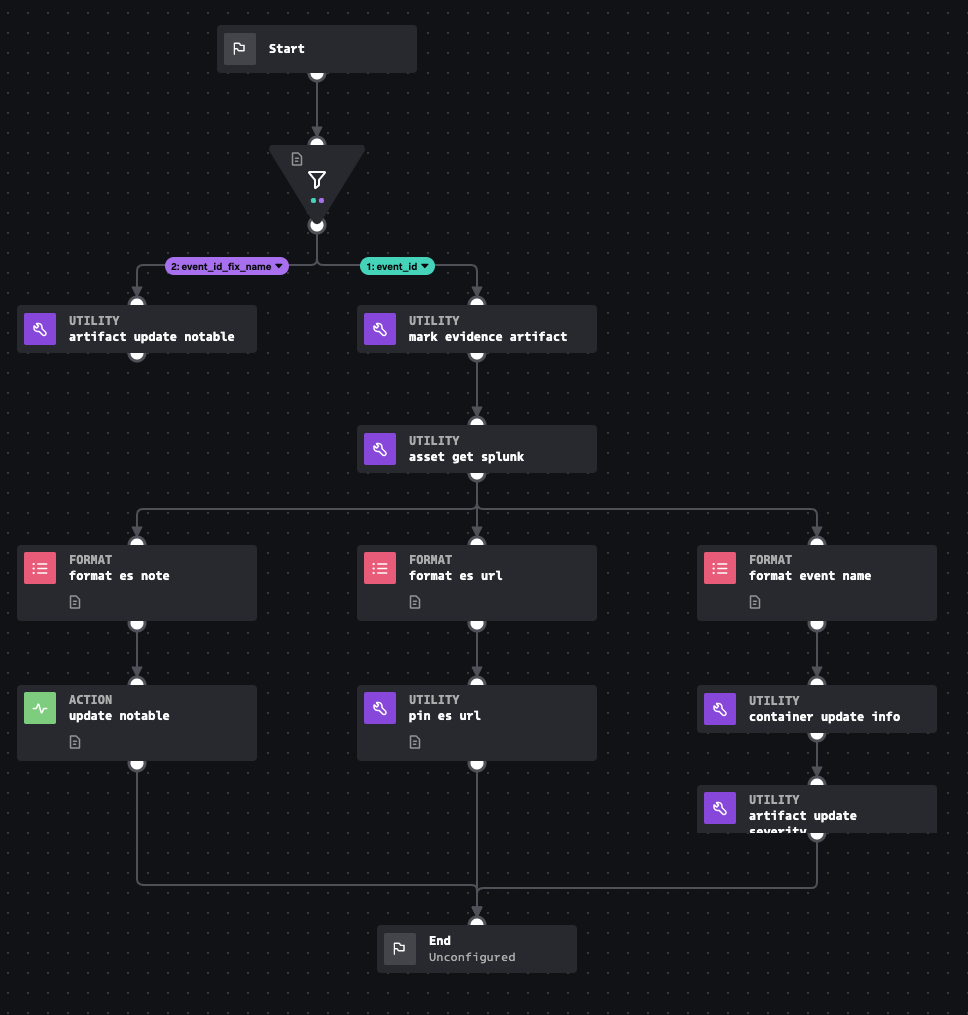
Playbook: Risk Notable Preprocess
Description
"This playbook prepares a risk notable for investigation by performing the following tasks: 1. Ensures that a risk notable links back to the original notable event with a card pinned to the HUD. 2. Posts a link to this container in the comment field of Splunk ES. 3. Updates the container name, description, and severity to reflect the data in the notable artifact."
Apps
How To Implement
For detailed implementation see https://help.splunk.com/en/splunk-enterprise-security-8/security-content-update/how-to-use-splunk-security-content/5.8/use-splunk-soar-playbooks-and-workbooks-from-the-risk-notable-playbook-pack/get-started-with-the-risk-notable-playbook-pack-for-splunk-soar
Explore Playbook
Click the playbook screenshot to explore in more detail!
Required fields
-
event_id
-
info_min_time
-
info_max_time
Reference
source | version: 1