Playbook: Splunk Message Identifier Activity Analysis
Description
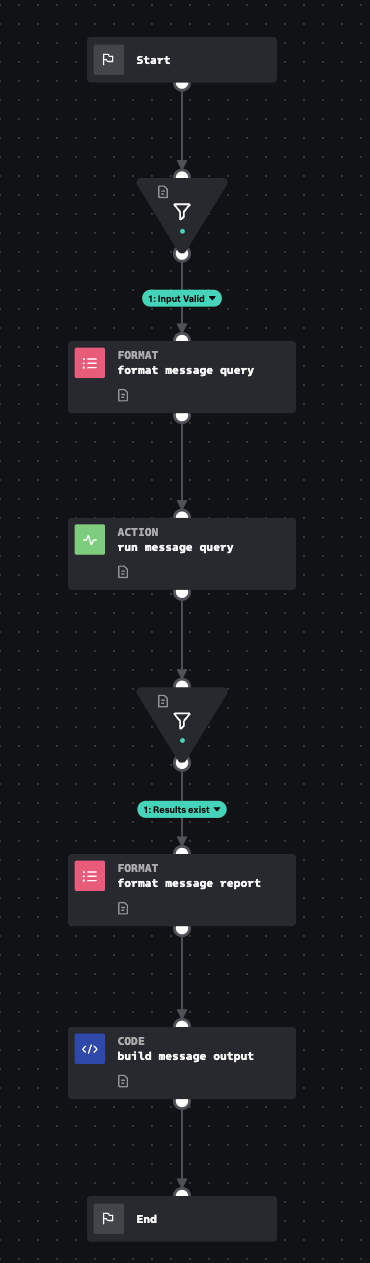
Accepts an internet message id, and asks Splunk to look for records that have a matching internet message id. It then produces a normalized output and summary table.
Apps
How To Implement
This input playbook requires the Splunk connector to be configured. You will also need data populating the Email.All_Email datamodel in the out-of-the-box configuration of this playbook.
Explore Playbook
Click the playbook screenshot to explore in more detail!
Reference
source | version: 1