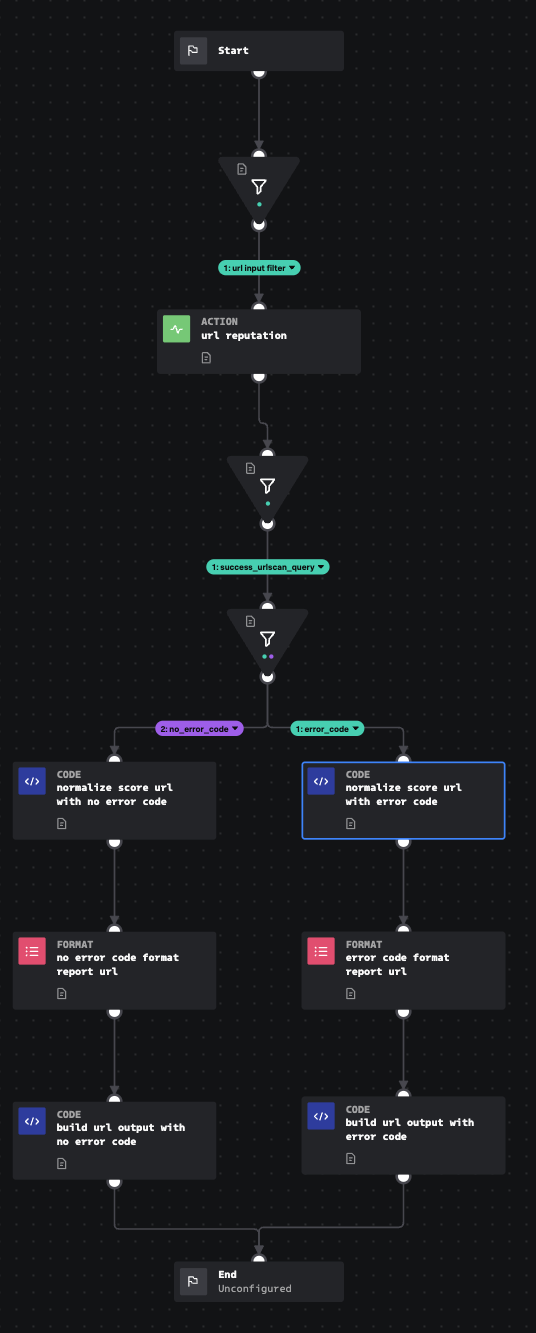
Playbook: UrlScan IO Dynamic Analysis
Description
Accepts a url link, IP, or domain to be detonated using urlscan.io API connector.
Apps
How To Implement
This input playbook requires the urlscan.io API connector to be configured. It is designed to work in conjunction with the Dynamic Attribute Lookup playbook or other playbooks in the same style.
Explore Playbook
Click the playbook screenshot to explore in more detail!
Reference
source | version: 2