Welcome to Splunk Security Content
This project gives you access to our repository of Analytic Stories that are security guides which provide background on TTPs, mapped to the MITRE framework, the Lockheed Martin Kill Chain, and CIS controls. They include Splunk searches, machine-learning algorithms, and Splunk SOAR playbooks (where available)—all designed to work together to detect, investigate, and respond to threats.
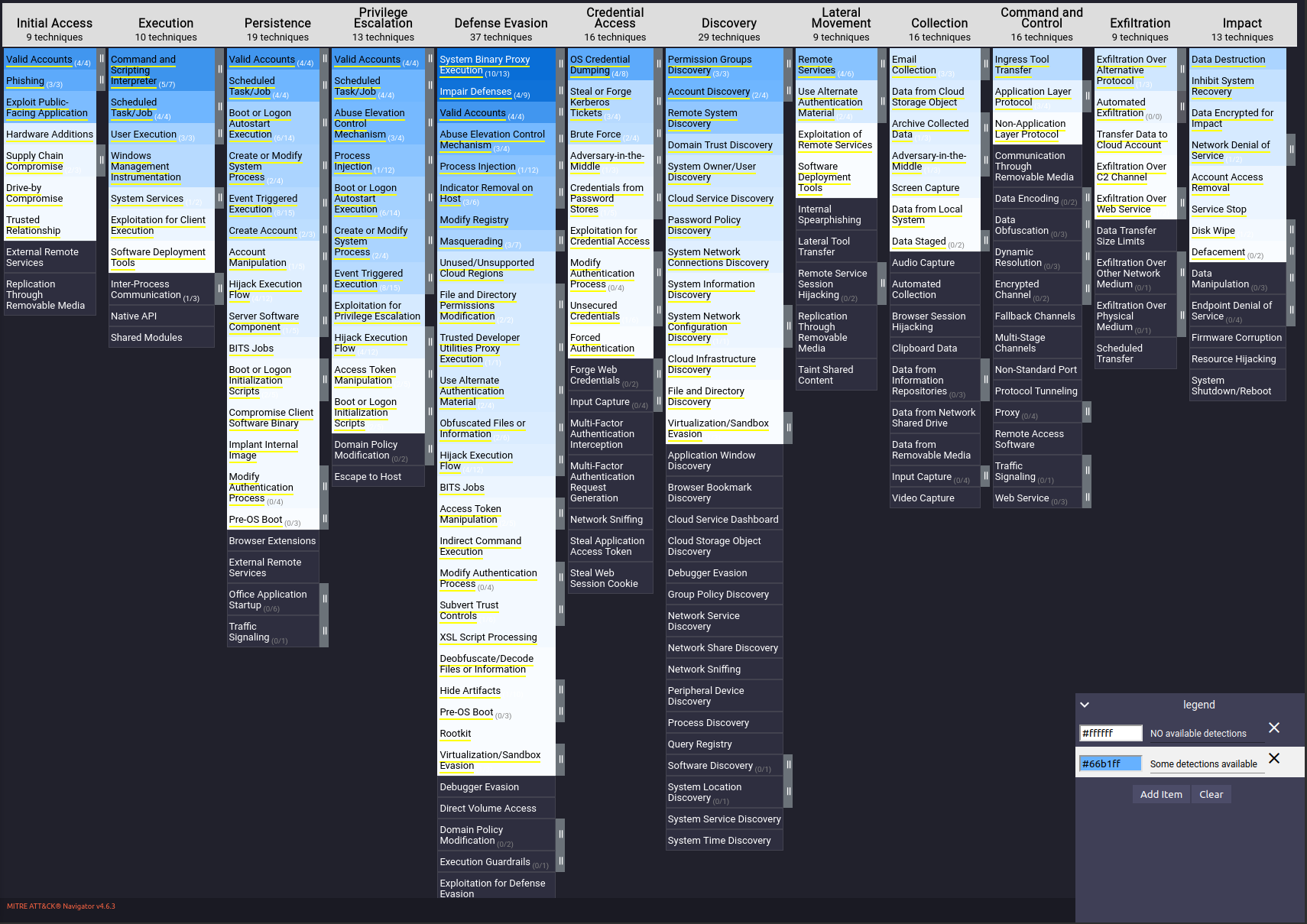
Detection Coverage 🗺️
Below is a snapshot in time of what technique we currently have some detection coverage for. The darker the shade of blue the more detections we have for this particular technique.
Questions? 📞
Please use the GitHub issue tracker to submit bugs or request features.
If you have questions or need support, you can:
- Join the #security-research room in the Splunk Slack channel
- Post a question to Splunk Answers
- If you are a Splunk Enterprise customer with a valid support entitlement contract and have a Splunk-related question, you can also open a support case on the https://www.splunk.com/ support portal
Contribute Content 🥰
If you want to help the rest of the security community by sharing your own detections, see our contributor guide for more information on how to get involved!